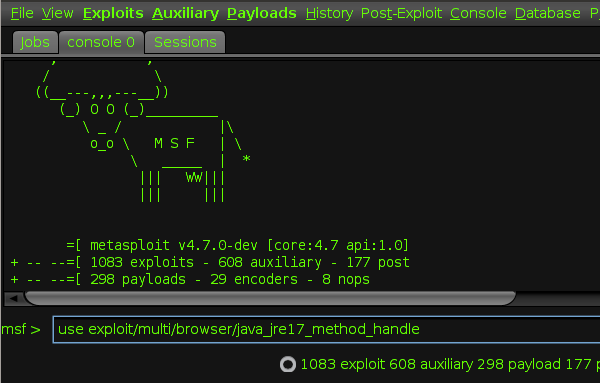
I was playing with Metasploit Framework and I was using the msfvenom payload. For that purpose I was using Kali Linux as a Virtual Machine, mainly because all the tools are pre-installed there. Running a Virtual Machine is not as easy as running the tools in a host Operating System. The available RAM of course is much less than the actual host and some times configuring things can be complex.
Nmap (Free)
Mar 26, 2020 Wireshark is famous among ethical hackers because it is one of the best hacking software for windows 10 and other OS. It is primarily a packet crafting tool that allows you to probe firewall rules and discover the weaknesses of any network quite quickly. 20 Best Hacking Tools For Windows, Linux, and Mac OS X in 2021. Rather than calling Metasploit a collection of exploit tools, I’ll call it an infrastructure that you can utilize to build your custom. Quick Access Tool Bar In Excell 2013 For Mac 3uTools- The ultimate all-in-one tool for flashing and jailbreaking iPhone, iPad and iPod Touch - Duration: 17:54. Dinh Ngoc An 89,639 views. 3uTools is a free tool that helps you jailbreak your iOS device (iPhone, iPad and iPod) and do a lot more things with it.
'Our goal was to make Mac OS X a first-class target for Metasploit.' Metasploit is an open-source toolkit that makes it easy for hackers to launch a barrage of attacks against a computer system. 7 Best Hacking Tools. Ever since you enter the field of Ethical Hacking, you always want to have your hands get on most of the Hacking Tools. More tools you know, more your hacking career is about to fly off. So let’s discuss the best 5 hacking tools. It is a free and open-source tool that is used for network discovery and security.
Nmap is the best port scanning tool you can use and also open source. Used widely, mainly because of the incredible power and flexibility it offers. On Mac OS Nmap comes with ZenMap, in the installation pack. For those who don’t like the terminal Zenmap is the perfect tool. I prefer using Nmap but in some cases, like for example when you have multiple hosts to scan, Zenmap makes reading them much easier.

Installation of Nmap is really simple and it does not require any typing at all. You can just download a .dmg file from the official website and do a normal installation like in every other application.
Links: Nmap – Github
Nikto (Free)
Nikto comes pre-installed on Kali Linux and some times it can help you find some hidden Gems on the web server you are testing. Nikto is a Web Server scanner that will inform you in case there is an outdated software version, if it finds some insecure or default files / directories and about some possible server misconfigurations.
In order to install Nikto you need to install Homebrew. To install Homebrew you need to type a single command on your terminal.
After installation if you didn’t agree with the Terms of Service of X-Code you will probably need to follow the instuctions. The instructions are pretty clear and simple to follow. Next you have to install Nikto. Go back to your terminal and type the following.
After finishing the installation you will be able to scan every web server using the command nikto -h {URL}.
Links: Homebrew – Github – Nikto
Wireshark (Free)
The Wireshark is the most known Network Traffic Sniffer, that is open-source like all the tools so far. The Wireshark distribution also comes with TShark, which is aline-oriented sniffer (similar to Sun’s snoop, or tcpdump) that uses thesame dissection, capture-file reading and writing, and packet filteringcode as Wireshark, and with editcap, which is a program to read capturefiles and write the packets from that capture file, possibly in adifferent capture file format, and with some packets possibly removed from the capture.
Installation is pretty simple, since it come as a .dmg file and the installation is like on every other application on Mac OS. After installation a new icon will appear on the launchpad’s application list. From there just by clicking it you can start sniffing the network traffic, after specifying the interface you would like to intercept.
Links: Wireshark – Github
Sqlmap (Free)
The Sqlmap is a powerful tool for finding SQL injections. It is completely automated and just by specifying a parameter the tool will try to exploit the injectable parameter sometimes even without you having to specify the type of database. It supports multi databases including SQL and non-SQL databases. Installation is pretty simple by using brew.
When the installation is complete you can just type sqlmap on terminal to launch the tool.
Links: sqlmap – Github
Zed Attack Proxy (Free)
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds of international volunteers*. It can help you automatically find security vulnerabilities in your web applications while you are developing and testing your applications. Its also a great tool for experienced pentesters to use for manual security testing.
The easiest way to install ZAP is by using brew. Start by installing caskroom.
After the installation is complete the system is ready to install ZAP.
After the installation is complete a new ZAP icon will appear on the launchpad.
Links: OWASP ZAP – Github
Burp Suite (Free / Paid)
My personally favourite proxy tool is Burp Suite. It offers pretty much the same options as ZAP, with better and much easier to use design. This is only for the Community version. The paid version offers automated fuzzing, with good results, it offers Intruder, a function to repeat requests for fuzzing, with custom wordlist, support for regular expressions and much more. Intruder is also available for the Community version, but it has a throttling that can be a bit slow. Installing Burp is really easy, you just need to visit their website and they offer an option for Mac OS, and you just download an install the .dmg file.
Links: Burp Suite
Aircrack-ng
Unluckily the tool for every Wi-Fi pentration testing is partially available on OS X. You can do a really simple installation of the Aircrack-ng with macports, but Airodump-ng and Aireplay-ng are linux only and will not work under OS X native, so for reinjecting and sniffing you will have to use other means.
After finishing the installation you can use it by typing aircrack-ng and the options you prefer.
Links: Aircrack-ng – Github
TestSSL (Free)
TestSSL is the best tool to test the SSL configuration of the server you are testing. What I like the most about TestSSL is the clean UI it offers and the simplicity in use. You get different results depending on the device you want to have as a reference and writes in really clean form the possible vulnerabilities of the current configuration.
To install TestSLL you firstly have to download the git repository from Github. Current stable version is 2.8.
Then go to the folder of TestSSL.
If you want to run TestSSL on a server you can just execute the .sh file followed by the URL of the website.

Links: TestSSL – Github
Wappalyzer (Free)
This browser extension is available for both Firefox and Chrome, giving users the ability to really easily identify technologies used on a Web Application. This simple plugin displays versions of web server servers, libraries, programming languages and more. What makes this plugin so helpful is it’s accuracy, how easy is it to use and of course it is open source. I find out about this plugin a few months back and I am using it extensively, so it is worth a shot.
Links: Firefox – Chrome – Github
Gobuster (Free)
Great tool for enumerating directories, files and DNS subdomains. What I like about Gobuster is the flexibility if offers with extensions, authentication and mainly support for multithreading. I was mainly using dirb for enumerating files and directories, but what was the biggest concern for me was the fact that dirb does not support multiple threads, and this makes the process really slower. Using brew is it easy to install Gobuster.
Links: Github
Hashcat (Free)
Great tool for password recovery. Supports almost every known hashing algorithm and masking for password guessing. It can fully utilize your Mac’s performance while it offers great support for GPUs.

Links: Hashcat – Github
Today, Wikileaks published more documents part of its Vault 7 CIA exposé series, revealing new manuals for three tools named Achilles, Aeris, and SeaPea, part of a larger CIA project named Imperial.
Each of the three tools has a different purpose, being developed to target only a specific set of operating systems.
Achilles
The first of these tools is named Achilles and this is a utility for trojanizing macOS DMG installers.
According to a one-page user guide released by WikiLeaks, Achilles allows an operator to bind an executable to a DMG file for a one-time execution.
Running the DMG file installs the original app, installs the payload, and then removes the payload from the DMG file. Using a one-time execution routine is typical to US cyber-intelligence, who are known to put a lot of effort into remaining undetected on targeted machines.
Aeris
The second CIA hacking tool manual released today is for a tool called Aeris, which is an implant (malware) for POSIX systems.
According to the document, Aeris is written in C and can work on the following operating systems:
Debian Linux 7 (amd64)
Debian Linux 7 (ARM)
Red Hat Enterprise Linux 6 (i386)
Red Hat Enterprise Linux 6 (amd64)
Solaris 11 (i386)
Solaris 11 (SPARC)
FreeBSD 8 (i386)
FreeBSD 8 (amd64)
CentOS 5.3 (i386)
CentOS 5.7 (i386)
Hacking Tool For Mac Os Catalina
Under the hood, Aeris includes features specific to data exfiltration utilities, usually used to steal information from targeted hosts via secure TLS-encrypted channels.
The Aeris manual doesn't include details of how the data is collected, most likely meaning its part of a larger attack chain and CIA operators must use other tools to compromise systems, identify desired data, download Aeris, and only then exfiltrate any collected information.
Hack App Store Mac Os X
SeaPea

The third and final manual released today is for an OS X rootkit named SeaPea. This tool's manual was previously released in another WikiLeaks CIA dump named DarkSeaSkies, a collection of tools for hacking Macs and iPhones, released in March.
To review, SeaPea provides CIA operators with a kernel-level implant that allows them to persist infections on OS X systems between system reboots.
Hacking Tool For Mac Os 10.13
Additional capabilities include the ability to hides files or directories, start socket connections or launch desired (malicious?) processes.
The SeaPea manual is old, being dated to the summer of 2011, and lists as 'tested operating systems' two very old OS X versions — Mac OS X 10.6 (Snow Leopard) and Mac OS X 10.7 (Lion).
Today's dump is part of a larger series called Vault 7 contains documents WikiLeaks claims were stolen from the CIA by hackers and insiders. You can follow the rest of our WikiLeaks Vault 7 coverage here. Below is a list of the most notable WikiLeaks 'Vault 7' dumps:
ᗙ Fine Dining - a collection of fake, malware-laced apps
ᗙ Grasshopper - a builder for Windows malware
ᗙ DarkSeaSkies - tools for hacking iPhones and Macs
ᗙ Scribble - beaconing system for Office documents
ᗙ Archimedes - a tool for performing MitM attacks
ᗙ AfterMidnight and Assassin - malware frameworks for Windows
ᗙ Athena - a malware framework co-developed with a US company
ᗙ Pandemic - a tool for replacing legitimate files with malware
ᗙ CherryBlossom - a tool for hacking SOHO WiFi routers
ᗙ Brutal Kangaroo - a tool for hacking air-gapped networks
ᗙ ELSA - malware for geo-tracking Windows users
ᗙ OutlawCountry - CIA tool for hacking Linux systems
ᗙ BothanSpy & Gyrfalcon - CIA malware for stealing SSH logins
ᗙ HighRise - Android app for intercepting & redirecting SMS data